
API Google Referrer помогает бороться с мошенничеством в мобильных сетях

Google Play Referrer — это стандартный, но очень надежный и точный способ атрибуции конверсий через Google Play (но не из магазина Android). Он позволяет поставщику атрибуции отслеживать статистику и отправлять ее параметры в магазин, а затем получать их обратно при загрузке приложения.
Но мошенники постоянно ищут новые способы перехитрить защиту – например, они обнаружили лазейку в методе Referrer API, которую можно использовать для перехвата установок.
В отличие от ботов или поведенческих аномалий, перехват установки компрометирует атрибуцию реальной установки от реального пользователя. При таком мошенничестве вредоносный код отправляет ложные «партнерские» данные в SDK поставщика измерений или атрибуции, пытаясь присвоить оплату за установку приложения себе.
Новый Google Referrer API, разработанный в сотрудничестве с нашими партнерами в Google, закрывает эту брешь, аутентифицируя данные партнера и активно блокируя внедрение поддельных партнерских данных.
Насколько эффективен будет новый Google Referrer API в борьбе с мошенничеством?
Мы видим многочисленные попытки мошенничества, направленные на платформы атрибуции в играх путем внедрения кликов после начала загрузки. Особенно часто это встречается в азиатских кампаниях.
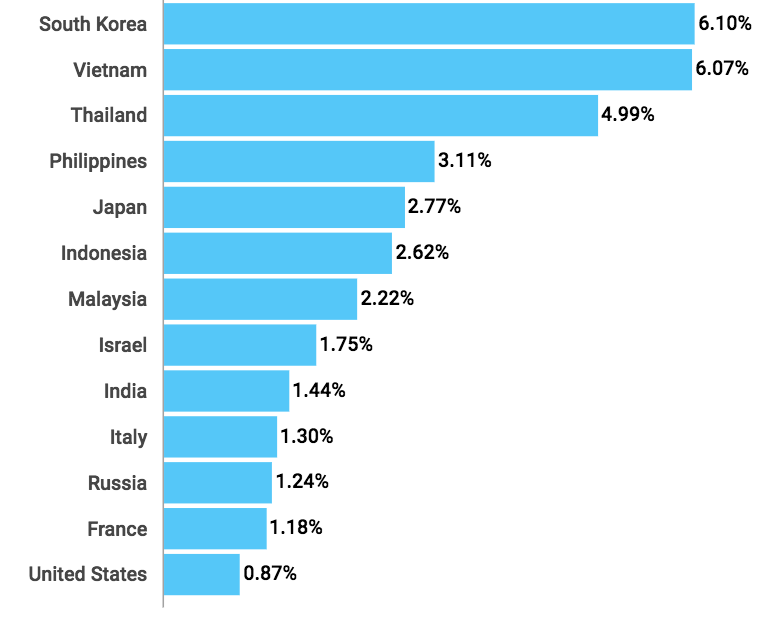
Перехваты партнерских установок по странам
Что касается тематических категорий, то больше всех страдает финансовая отрасль, на втором месте – лайфстайл. Негативное влияние на гейминг-сферу относительно невелико, вероятно из-за более низкого в этом сегменте показателя CPI, который не так привлекателен для мошенников. Кроме того, маркетологи игровых приложений в большинстве своем — это опытные и технически подкованные специалисты, они используют сильные защитные механизмы чаще, чем их коллеги из других тематических отраслей.
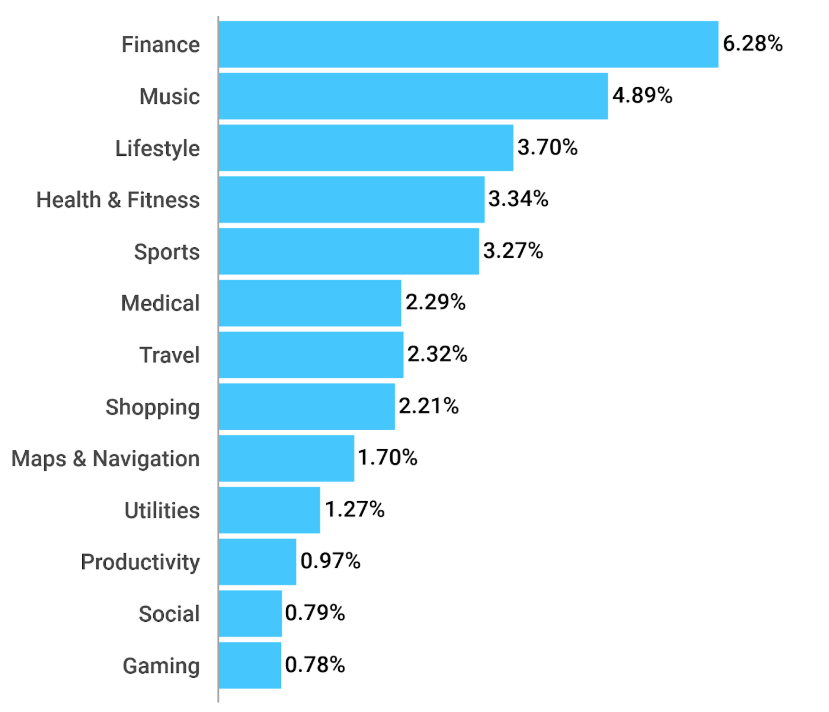
Перехваты партнерских установок по категориям
Прозрачность, точность и глубокий анализ
Понимание того, какой путь проделывают ваши пользователи между нажатием на партнерскую ссылку Google и установкой вашего приложения, будет крайне важно для обнаружения и блокировки перехвата установки, это также поможет вам принимать более взвешенные решения о развитии продукта и его маркетинге.
Вот почему AppsFlyer обеспечивает комплексные отчеты о перехвате партнерских установок на дашборде Protect360 и делает новые данные в Play Store доступными для отчетов с сырыми данными.
Эти новые данные Play Store содержат:
- Строку партнерских данных (URL-адрес) установленного пакета
- Метку времени (в секундах) о моменте нажатия партнерской ссылки
- Метку времени (в секундах) о моменте начала процесса установки (загрузки)
Почему данные о партнерских ссылках Google так важны:
- Повышают точность обнаружения и блокировки рекламного мошенничества.
- Предоставляют более глубокий и подробный анализ: вы будете точно знать, мошенничество какого типа было заблокировано и почему.
- Дают более четкое понимание пути пользователя: в прошлом единственными доступными моментами были время нажатия и время установки, а добавление новых моментов дает больше информации о пути клиентов мобильных приложений.
- Обеспечивают доступность информации о строке источника ссылки. Это означает, что мошенники больше не могут имитировать URL-адрес партнерской ссылки.
- Дают больше определенности за пределами показателя CTIT: стандартный анализ для поиска перехвата установок по показателю времени от нажатия до установки (CTIT) обычно ориентирован на поиск большого числа установок в течение первых 2-5 секунд после нажатия, но некоторые приложения устанавливаются медленнее, чем другие. Анализируя весь путь пользователей — нажатие, загрузка, первое открытие приложения — вы сможете принимать более обоснованные решения и настраивать свой показатель CTIT на основе поведения ваших пользователей.


