Click flooding
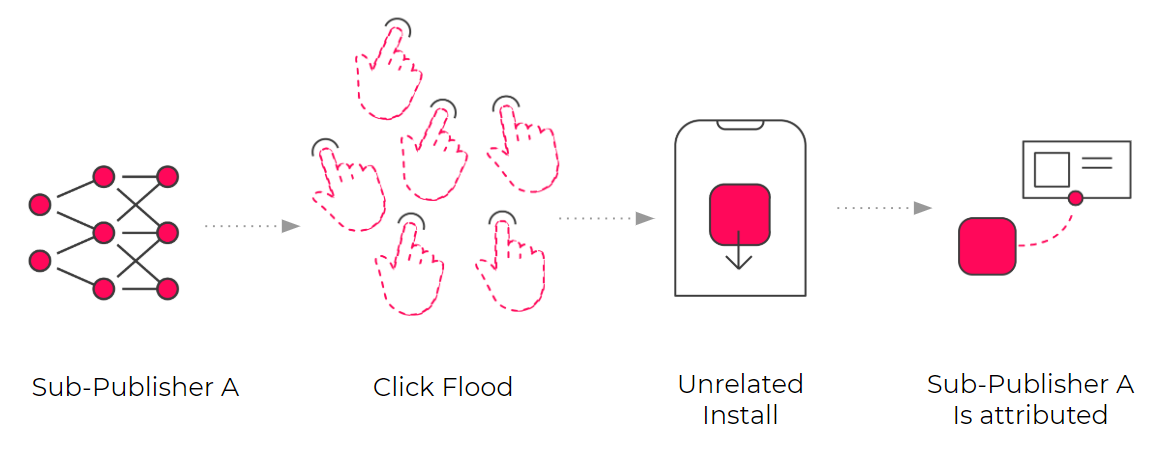
Click flooding is a type of mobile ad fraud that occurs when networks intentionally report a large number of fraudulent clicks in hopes of taking credit for the last click before an app install happens, so that they can take all the credit.
What is click flooding?
Click flooding (also known click spamming) is a type of click fraud and occurs when bad actors send large numbers of fraudulent click reports in the hopes of delivering the last-click prior to installs to get paid out by advertisers and decimate marketing budgets.
How does click flooding work?
The fraudster will try and execute clicks for users who haven’t made them, claiming credit for fake clicks.
A fraudulent app could be executing clicks while the user engages with it, or while active in the background (battery savers, launchers etc.). The app could even report impressions as clicks to present false engagement, all without the user’s intent or knowledge.
How to block click flooding fraud:
Anti-fraud solutions automatically block traffic from click flood sources.
To identify a source perpetrating a click flooding attack, they identify traffic with long CTIT distribution rates, low click-to-install conversion rates, and/or high multi-touch contributor rates (note: this requires multi-touch attribution data).
A helpful general benchmark when examining your own data is that about 75% of installs occur during the first hour following a click, and 94% of installs occur within 24 hours following a click.
Video ads and large apps often have longer CTIT.
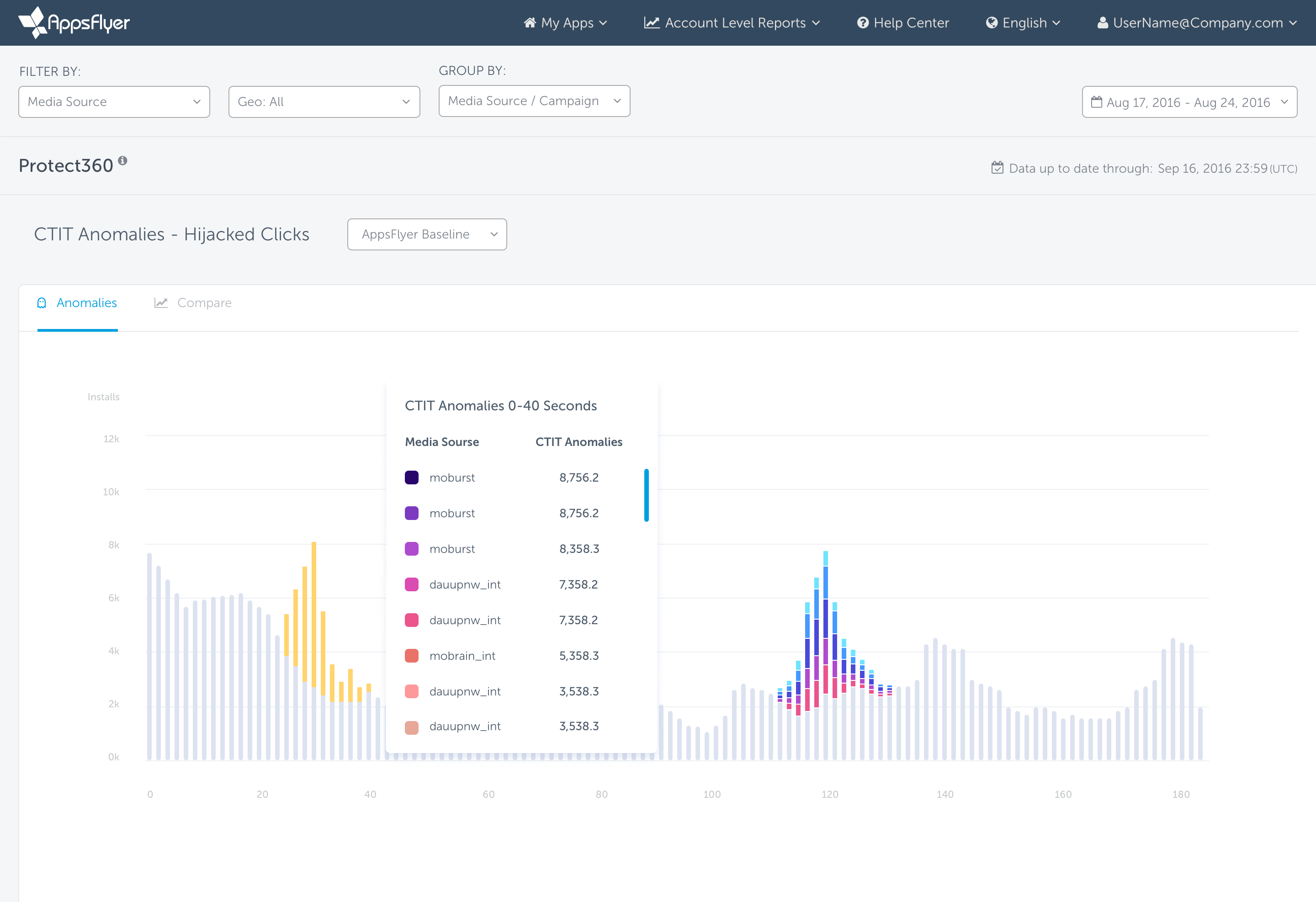
Here’s an example of how you might identify CTIT anomalies using AppsFlyer: