Everything you need to know about iOS 14+ fraud


The launch of Apple’s iOS 14 in April of 2021 sent the entire mobile marketing landscape into a realignment process.
Suddenly, a number of key elements were either removed or dramatically limited. User ID limitations, different measurement time frames, in addition to SKAdNetwork (SKAN) and its conversion values mechanism fundamentally changed the iOS landscape.
In an industry that is used to seeing its fair share of changes, most key stakeholders were quick to respond and adapt to the new reality.
Some decided to put their focus elsewhere and reallocate their marketing budgets, leading to a 25% decrease in iOS budgets, while others decided to take the innovative approach and modify their work methods to fit the new reality.
New products and solutions were introduced to the market in an effort to solve the market’s measurement concerns, but one key question has yet to be answered.
What is the state of ad fraud in iOS since the launch of iOS 14?
To answer this question, let’s try and make sense of what’s going on.
A multidimensional landscape
Since the release of iOS 14 the vast majority of installs attributed in SKAN originated from direct traffic sources, with the absolute majority of traffic coming from either self reporting networks (SRNs) and SDK networks.
SRN traffic includes well established media channels like Google and Facebook (and others), where, historically, fraud rates have been significantly lower than the industry average and almost 0% in iOS specifically.
Protect360 analyzes all traffic running through AppsFlyer’s ecosystem, regardless of its source, and SRNs are no different. However, their consistent maintenance of very low fraud rates over time, combined with the high level of communication and integration we have with such media partners puts them in the “safe traffic” category when it comes to mobile attribution fraud.
As for the rest of the sources active in SKAN, these can be segmented into two main types of media partners: SDK networks, accounting for 49% of SKAN traffic, and other sources that mainly include DSPs and ad networks.
While the latter group with its relatively low volume of traffic seem to only be testing the new waters, the leading SDK networks in the market are more keen to adapt to the new SKAN reality. This is still a relatively small group of media companies that are also fully integrated with AppsFlyer and have historically presented relatively clean traffic with much lower fraud rates than average.
These two media partner groups are currently dominating the SKAN landscape, which allows us to consider Apple’s new SKAN environment as “fraud free” at this point in time. Keep in mind that the data presented above reflects the current media mix and may very well change down the line, making constant vigilance a must.
However, iOS activity is not just SKAN. There’s still plenty of activity that is not (strictly) reliant on SKAN. In fact, it’s currently responsible for the majority of iOS activity, as the following chart shows:
To better understand this, let’s explore how measurement can be broken down in iOS.
iOS attribution measurement options
There are three types iOS attribution frameworks that are currently available for marketers:
- SKAN only
Mobile app campaign attribution that strictly relies on SKAN measurement. - MMP only
Attribution can be done either through ID matching for consented users (users who have allowed companies to share their IDFA), or through probabilistic modeling across all users. - Hybrid
Attribution will be done through a combination of the two types described above. In this scenario, networks continue sending engagement data to their MMP even for SKAN activity.
Example: when a publisher reports an ad view engagement by a certain user to SKAN, an impression URL will also be sent to the MMP
The hybrid model offers advertisers and media partners the benefit of leveraging many of AppsFlyer’s measurement capabilities, while aligning with Apple’s privacy requirements. However, it also creates an issue of double measurement records.To solve this problem, we recently launched our Single Source of Truth (SSoT) solution. Whenever an install attribution is recorded by both AppsFlyer and SKAN, AppsFlyer will only record the attribution once by a unique process of deduplication. This presents our clients with reliable and accurate single truth reality of their activity.
Monitoring fraud in an era of limited data
AppsFlyer customers using Protect360 who also measure their iOS campaigns with probabilistic attribution (in hybrid or MMP only models), will continue to enjoy Protect360 fraud protection.
At the moment, nearly all Protect360 anti-fraud models and detection logic can be applied to probabilistic attribution models. Anti-fraud logic has evolved dramatically over the years and no longer relies on user identifiers to detect fraudulent behavior patterns.
Advanced detection techniques like Bayesian networks give Protect360 the ability to base anti-fraud logic on large scale behavior patterns and apply detection logic onto a single occurrence regardless of specific identity. These advanced machine learning based techniques learn from past events and apply sophisticated logic for future detection with maximal accuracy.
User cluster behavior, biometric analysis, and large scale statistical models apply multiple measurement techniques that correlate with probabilistic attribution models, while aligning with very strict accuracy thresholds to ensure minimal false positive cases.
Relying on AppsFlyer attribution also means advertisers have full transparency of engagement and install timestamp data. These not only play an important role in the fraud detection mechanism, but also provide greater value for advertisers since they can be leveraged for further analysis and optimization.
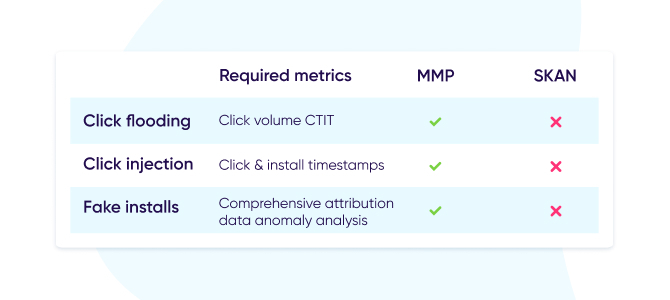
It is vital to understand that common fraud protection methods are fully covered by Protect360 in the new iOS landscape, while relying solely on SKAN will leave you significantly exposed. These methods include:
- Click flooding: The two basic metrics required for click flooding detection are click volume and the time between click and install (CTIT). This fraud can be detected with the complete click data that’s available through MMP and hybrid attribution.
SKAN doesn’t currently provide advertisers with full engagement data, making click flooding impossible to detect.
- Click injection: Detection of click injection fraud is mainly done through anomaly analysis across click and install timestamps. These signals are only available when MMP attribution is involved, as SKAN does not report any attribution timestamp data.
- Fake installs: Faking the entire attribution cycle through emulators, bots, or device farms can only be detected through a comprehensive analysis of all available measurement points like timestamps.
MMP attribution will ensure this data is reported and monitored by both the advertiser and Protect360.
Innovation powered vigilance
While the logic, models, and ability to detect fraud in the new iOS landscape are here, it’s imperative that all marketing parties take an active part in the reporting effort.
Advertisers and media partners should strive for an open and transparent relationship to make sure their best interests are kept, and fraud is eliminated from their relationship.
It is highly recommended to have AppsFlyer’s probabilistic attribution a part of every advertiser’s campaigns when heading into SKAN campaigns. This will not only enable Protect360’s fraud protection (for Protect360 customers), but also open up additional measurement capabilities and insights available through AppsFlyer’s SSoT and other great products.
Different SKAN fraud scenarios have long been identified and discussed by our team, with relevant technical fraud solutions to follow.
The Protect360 team, powered by AppsFlyer’s innovative solutions like SSoT, is keeping a close eye on iOS developments and the ecosystem at large, as we’re rapidly heading into a privacy-centric future.