Take our interactive product tour
See how easy it is to map conversion values and pull advanced SKAN reports. Take an interactive tour right inside AppsFlyer’s platform.
See how easy it is to map conversion values and pull advanced SKAN reports. Take an interactive tour right inside AppsFlyer’s platform.
Apple’s introduction of AppTrackingTransparency (ATT) made the digital marketing landscape more complicated. There are more data streams, increased duplication, and partial data. But, with the right technology on your side you can still achieve all of your marketing goals. Our iOS 14+ solutions take the complexity out of SKAdNetwork, while seamlessly aligning with Apple’s privacy guidelines.
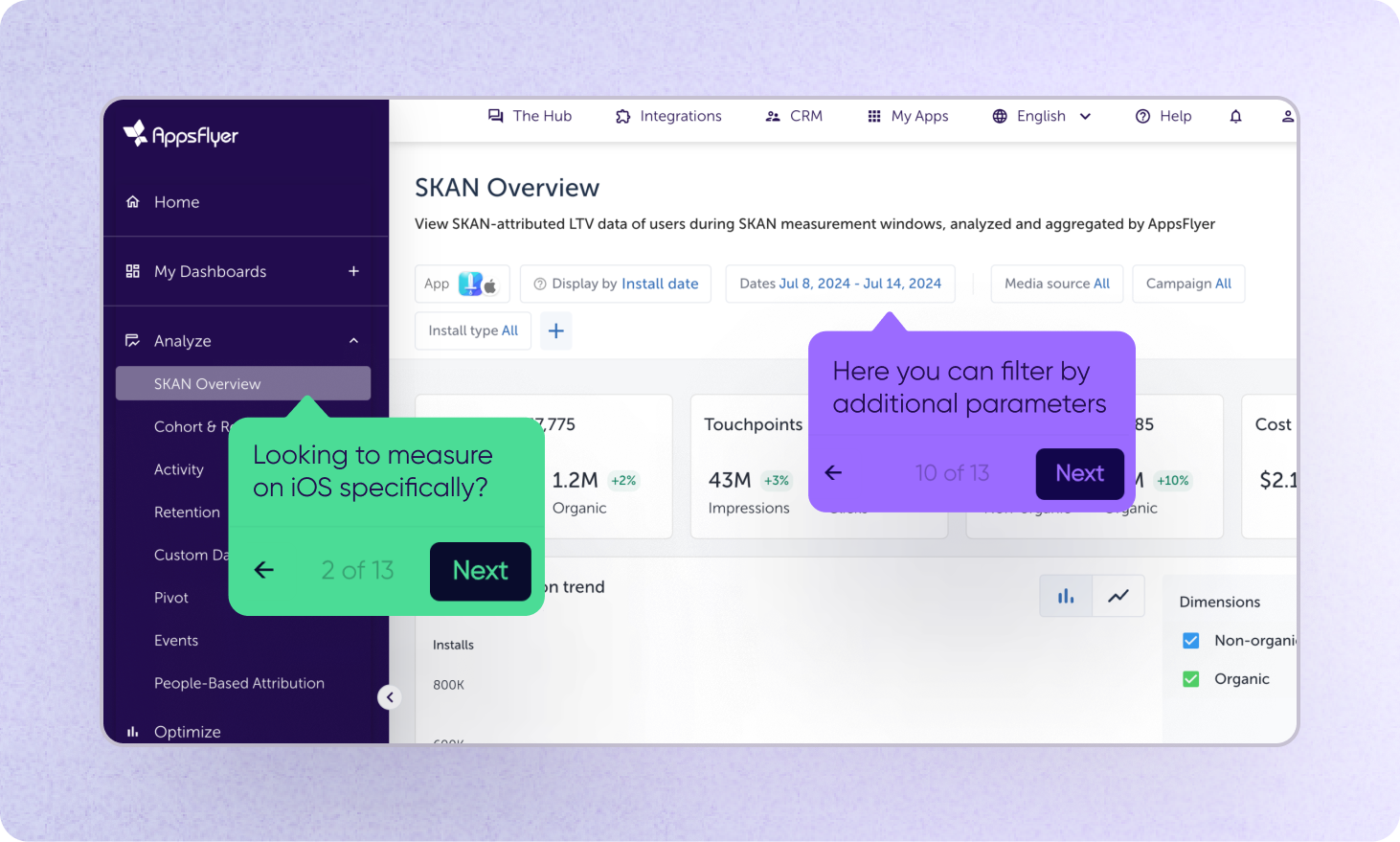
Discover how to harness the power of SKAdNetwork with our all-in-one solution. Our ever-evolving innovation helps brands make the complex aspects of SKAN attribution simple and accessible. From optimizing your strategy and fine-tuning conversion values, to predicting future campaign success, our solution gives you everything you need.
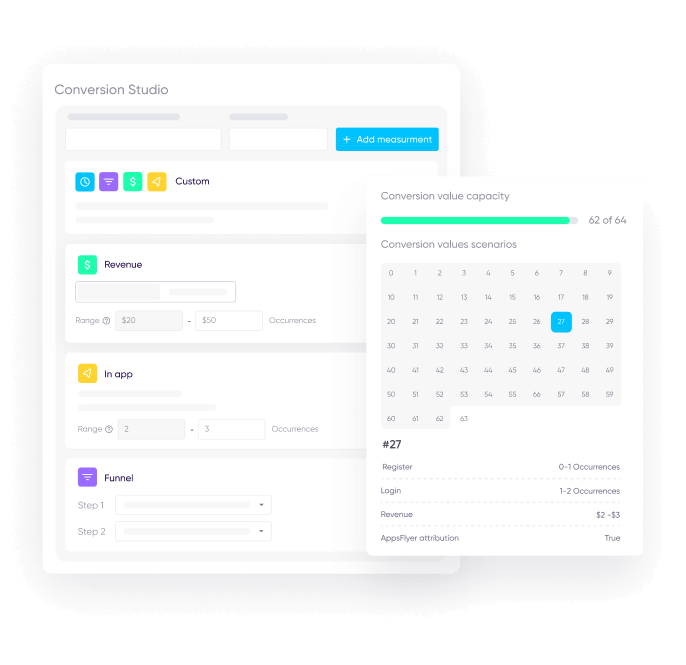
One of the most challenging aspects of SKAdNetwork is translating long-term performance measurement needs into complex conversion value maps. Our hyper-flexible conversion value mapping solution lets you focus on what you want to measure (retention, cohort, revenue, funnel progress and more) while leaving the technical aspects to us. You choose the performance metrics, we’ll help allocate the conversion values in the optimal way.
The introduction of SKAdNetwork decentralized data streams for iOS marketers, and its private-by-design mechanism means that incoming data cannot be deduplicated easily. We have developed a new way of attributing users that guarantees each user is only attributed once, helping marketers get a clear picture of campaign performance without compromising on user privacy.
Start optimizing your campaigns from day one with predictive analytics. Using advanced machine learning, predictive analytics lets you turn early user engagement activity into actionable insights.
Cut poor performing campaigns or boost good ones early on, to reduce waste and get the most from your budget.
Our 360° approach to iOS 14+ provides the industry’s most advanced and comprehensive measurement solution for analyzing, optimizing, protecting, and even predicting iOS 14+ campaign performance.
Comply with all iOS 14+ privacy regulations while getting accurate and actionable insights
Analyze your app’s ATT opt-in rates and how they perform against industry benchmarks
Get visibility into SKAN performance KPIs, including CVR, ROI, CPI, ARPU, ROAS, eCPA
Maximize conversion values’ potential with a flexible conversion value mapping tool

Model missing pieces like masked conversion values and future LTV based on your own data.